Hello Dear Friends, in this blog we will cover Information Security Elements in detail. Nowadays cyber (Computer Culture) crime where InfoTech is changing every second, we must prioritize the security of our digital information/assets over the security of our physical assets because we are living in an era when digital asset theft is significantly higher than physical asset theft. This is primarily because digital assets like cryptocurrencies and online accounts are stored on the server and accessible via the internet, making them more vulnerable to cyber-attacks like hacking and phishing scams. Furthermore, while physical assets typically require multiple thefts to accumulate a comparable value, digital assets can be stolen in large quantities with a single successful attack.
Information Security Elements in Daily Life:
These days you may have uttered that many organizations and individuals are becoming victims of cyber-attacks in which they can suffer significant financial and reputational loss, operational disruption, legal and regulatory ramifications, productivity decline, or individuals can suffer in losing their personal information, social media, and bank account details, privacy, and can affect health with stress and trauma. Some people work hard to create their website, application, or YouTube channel, but due to a lack of awareness about the dark side of the digital age or a lack of understanding about protective measures to secure their digital information, they may lose everything in a matter of seconds. A few instances are shared in below picture cuts.
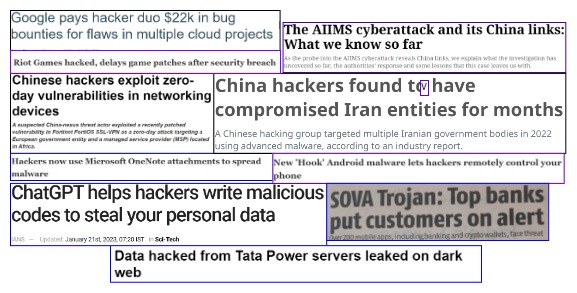
Are you terrified of these attacks because you fear you’ll become the next victim? Who knows, you might be the next honeypot, in which case one slip-up might spell significant catastrophes for your family and organization.
So, my dear friend, in order to secure our digital information and prevent ourselves from being victims of hackers, let’s shift our strong intention and attention and take some time together.
Table of Content-:
- What is Information Security (InfoSec)
- Objectives of InfoSec
- Information Security vs Cyber Security
- Protective Measure
What is InfoSec-:
Let’s first discuss the differences between Data and Information. In the world of computers, data can be any unprocessed, unorganized content that is stored in various formats, such as spreadsheets, text files, databases, etc. also It exists in various forms such as numbers, pictures, text, and audio. Information is a set of data that has been properly processed and organized to impart knowledge to readers and presented in a way that gives it context and meaning. Also, we can say that Information is data that has been transformed into something so that it is pertinent and valuable for the individual or organization that needs it.
So, every piece of data is not information but the information is a set of data that is processed, organized, and presented in such a way that it can be understood and used by the person who needs it.
Hope till now we have understood the real meaning of information and determined why it has to be secured, and why the term “Information Security” is significant.
So proactively taking steps to protect the three elements of information security Confidentiality, Integrity, and Availability (CIA) of our sensitive Information from unauthorized access, inspection, modification, disruption or destruction, etc. is known as Information Security. The goal of Information Security is to ensure the safety and privacy of our processed and structured data.
Three Elements CIA Triad of Information Security-:
Let’s now scrutinize the CIA triad. In essence, the CIA is a pillar of information security or, to put it another way, it is the goals of information security that must be met while safeguarding our vital information.
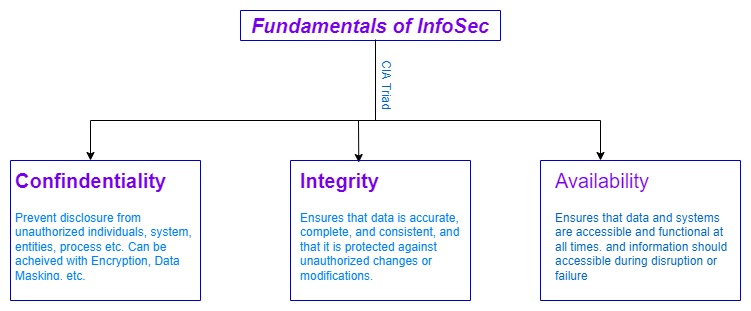
CIA stands for Confidentiality Integrity and Availability these are the three basic elements of information security as discussed above these are the basic elements of information security in addition to that we have more parameters that are also quite important while securing the information which is Non-Repudiation, Authenticity & Accountability.
Confidentiality-:
Confidentiality means effectively preventing unauthorized access to or disclosure of sensitive information. It makes sure that only permitted users or systems can access and view the processed data. Below is the best method adopted to achieve the confidentiality of information.
Encryption-:
Strong encryption to prevent the decryption of stolen information.
Access Control-:
password authentication, biometric authentication, and role-based access will inhibit unauthorized access and permits only authorized users or system can access information. Cloud Active Directory solutions can centralize and streamline access control across an organization’s resources.
Data Leakage Prevention (DLP)-:
Information that can be copied, uploaded, or shared via e-mail can be prevented with DLP software and hardware.
Data Masking-:
it is a technique of replacing information with fallacious data or symbols to obfuscate it.
Secure Communications-:
use of secure communications protocols to prevent eavesdropping and tampering of data during transmission.
Auditing & Monitoring-:
Logs and alerts can be set up to keep track of who accessing sensitive data and to spot any unusual activity.
The above short-discussed technique can be implemented to prevent unauthorized access to information.
Integrity-:
Integrity refers to the assurance that information must be modified or tampered with only authorization. It helps to ensure that information is reliable, consistent, and accurate as well as secure from unauthorized alteration or modifications. Below methods are adopted to achieve the goals of Integrity.
Hashing-:
Creates a unique digital fingerprint of the data, called a hash. The data will produce a different hash if it is altered in any way, making it easier to determine whether the data has been tampered with or replaced.
Access Control-:
It makes sure that data can only be updated by approved systems or members. This includes techniques like biometric authentication, role-based access control, & username-and-password authentication.
Input Validation-:
It is a technique used to assure the consistency, accuracy, and completeness of data inputted into a system. It may contain techniques like format validation, range validation, and data type validation.
Digital Signatures-:
Encrypting the hash of the data with a private key ensures the authenticity and integrity of digital documents. This also ensures that the data was not tampered with and came from the mentioned sender.
Data Backup & Recovery-:
Data can be recovered if an unauthorized change or deletion occurs with the help of regular data backups and a disaster recovery plan.
Auditing & Monitoring-:
Integrity violations can be found and looked into using auditing and monitoring. Logs and alerts can be set up to keep track of who accessing sensitive data and to spot any unusual activity.
The above shortly discussed methods can be used, the data’s integrity is protected and unauthorized alterations are avoided. It’s crucial to remember that Integrity and Confidentiality are intertwined and frequently applied as a team to safeguard the overall security of the data.
Availability-:
Refers to the information that must be available & functional at all times to the authorized users. It should be accessible to any authorized user or system when they need it. below are a few methods to achieve it.
Redundancy-:
Refers to the practice of maintaining multiple copies of data or systems so that users are not affected in the event of a failure or downtime. This can be accomplished through data replication, load balancing, and failover systems.
Backup & Disaster Recovery-:
In the event of a failover, a regular backup aids with quick service restoration.
Monitoring & Maintenance-:
Data and system monitoring and upkeep on a regular basis aid in spotting and fixing any potential problems before they arise.
Network & Infrastructure-:
It is essential to have a reliable network and infrastructure. By using a load balancer, redundant hardware, and network connections, as well as power and cooling systems, we can make sure that the data and systems are always accessible and functional, even when there is a heavy load or any failure.
Cloud Computing-:
Can be adopted as it provides high availability.
Fundamentals of Information Security
Let us dig a little bit more about InfoSec by understanding other fundamentals such as Non-Repudiation, Accountability, and Authenticity.
- Non-Repudiation-: Inability to refute the truth is referred to as non-repudiation. It is assurance that someone cannot deny the validity of something. or in other words, we can say that It provides the ability to demonstrate that a particular person or system carried out a particular action or transaction and that it cannot be later denied or repudiated by the person or system. It makes sure that any disputes can be settled as well as the veracity and integrity of electronic transactions and communications. This can be achieved with help of Hash-Based Message Authentication Codes (HMAC), Digital Signatures, Time-stamping, and Public Key Infrastructure (PKI).
- Accountability-: Means that it should be possible to connect a specific set of actions to a particular entity. In order to prevent fraud, data breaches, and other security threats, it makes sure that specific actions or transactions can be traced and attributed to a particular person or system.
- Authenticity-: Authentication is the process of verifying that a user or system is trustworthy or genuine, and authenticity provides the ability to demonstrate that a digital entity such as a message or file is trusted and received from claimed sender. This can be achieved with the following methods.
Authentication protocols such as oAuth, and SAML.
Cryptographic Algorithms such as AES, RSA, and others.
also, authenticity can be proved with a digital signature, Public Key Infrastructure (PKI), Hashing, Timestamping
Information Security vs Cyber Security
I believe we now understand what information security is, what its fundamentals are, and how to achieve them. Information security is a broad field that covers all the aspects such as endpoint security, network security, and physical security, also provides information assurance so that information can’t be tampered with or altered by unauthorized users or systems. whereas Cyber security is a subcategory of information security that focuses on technology-related threats, protecting servers, endpoints, databases, and networks by identifying gaps and misconfigurations that lead to vulnerabilities. It is a point of contention among tech professionals because the terms information security and cyber security are used interchangeably. To summaries, cyber security is concerned with protecting information in cyberspace, whereas information security is concerned with protecting data in cyberspace and beyond.
Protective Measures for organization
To help mitigate the risk of cyber-attacks and minimize the potential for losses, organizations must implement robust security measures such as firewalls, intrusion detection systems, and incident response plans. The following security measure can implement to secure the organization’s network.
EDR – Endpoint Detection & Response (EDR) is a software tool that is installed on the connected endpoint like PCs, servers, laptops, and other network devices which monitors them in real time and detects the malicious activity missed by the firewall by identifying registry change, and key file manipulation. However, endpoint agents can’t be deployed on BYOD, IoT devices, & cloud environments, etc.
XDR – Extended Detection & Response (XDR) is the advanced version of the EDR, it provides visibility across multiple data streams between endpoint, network, and cloud. Therefore, malicious files can be detected in the network flow.
NDR – Network Detection & Response (NDR) analyses the data packet in the network traffic rather than the endpoint or other data stream to detect any cyber threats and send a response to the IT team.
Strengthening of firewall policies
Regular Backup – to avoid downtime, data loss, financial loss
Training of staff with best practices of current cyberattacks faced by other organizations.
Protective Measures for Individuals
Individuals must be proactive in protecting their personal information and digital assets by employing strong, unique passwords and two-factor authentication, avoiding phishing scams (most common), and keeping their computer and mobile device software up to date. Individuals should also keep a close eye on their financial and personal information for any suspicious activity.

None